I completed and successfully defended my Ph.D. dissertation in May 2018.
Author Archives: lewis
Teaser
Poem
Research Updates
I’ve added new material to the site since the end of this 2012-2013 academic year:
- Field Statement (.DOC)
- Bibliography
Concepts and Critiques of Power
- Field Statement (.DOC)
- Bibliography
Dissertation Research
- Proposal (Draft, .PDF)
- Updated Bibliography
Internet Census
An anonymous researcher (one person though they use “we” throughout their documentation) has released the results of an extraordinary study. By temporarily constructing a botnet on openly available devices around the world, they were able to map usage of the global internet over IPv4 at a scope and level of detail that has no rival outside of proprietary network operations databases.
Continue reading
What's Wrong with CISPA?

What’s wrong with CISPA? (in as few words as possible)
As it’s written, CISPA won’t protect us from cyber threats, but it will violate our 4th Amendment right to privacy.
- It lets the government spy on you without a warrant. (read more)
- It makes it so you can’t even find out about it after the fact. (read more)
- It makes it so companies can’t be sued when they do illegal things with your data. (read more)
- It allows corporations to cyber-attack each other and individuals outside of the law. (read more)
- It makes every privacy policy on the web a moot point, and violates the 4th amendment. (read more)
Nostalgia for the present, well-spoken.
Omeka
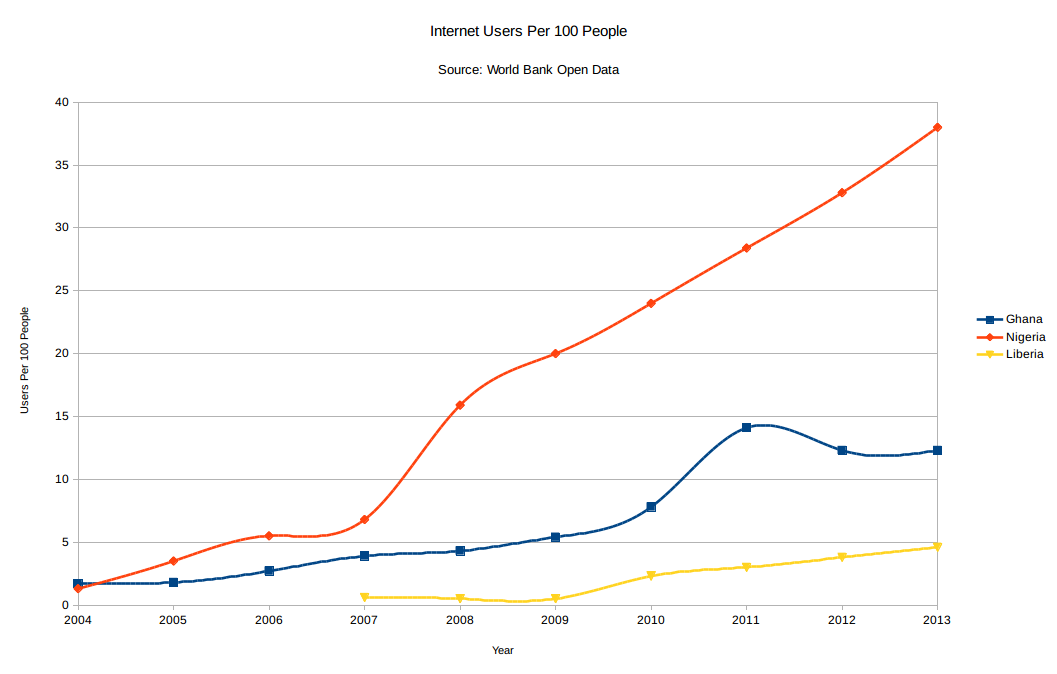
I’ll be using Omeka to collect and organize the myriad cultural objects that are beginning to congeal around my research into the internet in West Africa. This platform also plays really well with academic organizational conventions and even with bibliographic management software, like Zotero, which I love. For now I’m using the hosted version, at lewislevenberg.omeka.net — more to come there soon.
Research Updates
I’ve updated this site to reflect new material as of the end of this Fall 2012 semester:
New working copy of Internet Studies field statement
Updated bibliography for the field statement
New working copy of Critical Theories of Power field statement
Updated bibliography for the field statement

Research Paper – Nationalism, ICT Policy, West Africa
Nationalism in the Internet Architecture Policy of Western Equatorial Africa
DOWNLOAD THE ESSAY
Abstract:
This essay addresses the puzzle of how nationalism affects the deployment of internet architecture policy for these five countries. In particular, it examines how the institutions that support the creation and enforcement of internet policy draw on cultural concepts of nationality and internationalism, and how these compare to the practice of establishing an internet architecture. Questions it must answer along the way include how to understand nationalism in this context, what the primary institutions are in this context, and what the relationships between states, institutions, and populations are, regarding internet policy across the region. It shows that nationalism appears in the creation of policy and the stated scope of institutions that support and regulate the internet, largely driven by cultural factors. However, technologies themselves hold a less direct relationship to these factors. The physical architecture and practices of implementation remain separated from nationalist ideology, but the patterns of diffusion, adoption, and restructuring that take place political and financial terms do have a lasting effect on technology’s role in culture.